Security Program Considerations
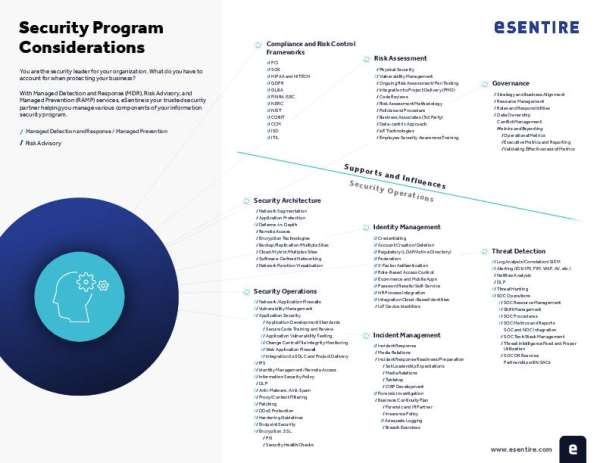
Security requires thinking beyond tools to assess visibility, governance, threat response, and readiness. This eBook guides security leaders through the critical considerations that define an effective MDR strategy. Download it now and use its insights to stay prepared. Follow up with JCMR Technology to discuss next steps for a more resilient security program.
Please enter your information below to view this content: